Cyber Security Course in Pune with Placement Support
 A comprehensive cybersecurity strategy has numerous layers of protection.
A comprehensive cybersecurity strategy has numerous layers of protection.  Prevention of cyber attacks is the primary goal of a Cyber expert.
Prevention of cyber attacks is the primary goal of a Cyber expert. An organization's people, processes, and technology must complement one another to effectively defend against cyber threats.
An organization's people, processes, and technology must complement one another to effectively defend against cyber threats.Start Today!
CONSULT WITH
OUR ADVISORS
- Course & Curriculum Details
- Flexible Learning Options
- Affordable Learning
- Enrollment Process
- Career Guidance
- Internship Opportunities
- General Communication
- Certification Benefits
Learning Curve for Cyber Security with Placement Support
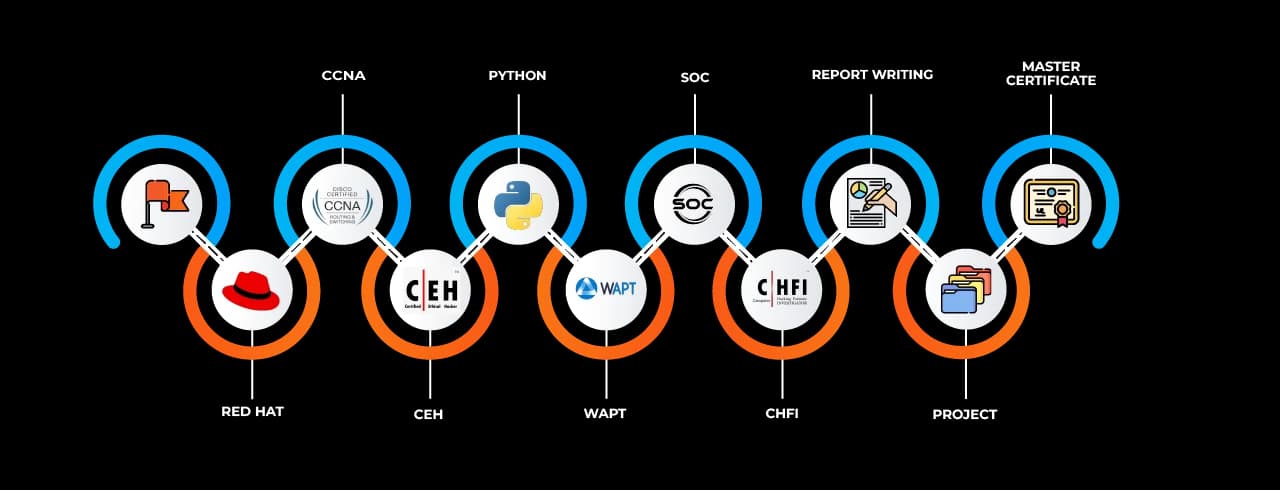
Master In Cyber Security with Placement Support Course
OneCourseMultipleRoles
Empower your career with in-demand data skills and open doors to top-tier opportunities.
Cyber Security Analyst
Malware Analysis
information security
SOC
Risk Analyst
cyber forensics & DFIR
Threat Intelligence Analyst
Compliance and Risk Analyst
Cloud Security Specialist
Cyber Security Consultant
Incident Response Specialist
-1744728435835.webp&w=3840&q=75)