Why is Choosing an Ethical Hacking Course in Pune the Smartest Career Move Right Now?
Enroll in an ethical hacking course in Pune, and you step right into the center of this growing industrial base, which also serves up real-time input from the market, which input programs don’t always provide.
Today’s focus of cyber defense training is not to just learn the tech terms; it is to put yourself in the arena of a large tech hub, which is very competitive and high-stakes. In Pune we see companies that are on the lookout for certified professionals who protect large data structures and who are also able to avert very serious operational disruptions. By building your tech base here, you also build connections with the local tech community and put yourself at the front of the hiring queue.
- Thriving IT Ecosystem: Training at the doorstep of major corporations and international tech players gives you an instant networking edge.
- High-Demand Job Market: Local businesses are out there looking for skilled white hat professionals to protect company assets and customer data.
- Real-World Enterprise Context: We prepare you for the tough digital world so you hit the ground running with real large-scale network issues from day one.
What Core Concepts are Covered in the Best Ethical Hacking Classes in Pune?
Entering the field of defensive security may seem very off-putting if you do not have a structured plan to guide your study. , the best ethical hacking classes In Pune break that barrier down, by which we mean they take you through a very detailed, zero-to-hero learning path.
Once you get your base technical skills down, the curriculum shifts to a more in-depth and specialized study. We will be looking in depth into vulnerability assessments, system enumeration, and the latest in cybersecurity methods. Also a great deal of the instruction is on that which is right within what is legal and moral. You won’t just study what a cyber attack is; we will make you an expert in white hat techniques that fully neutralize threats, secure company systems, and also comply with global standards.
- Infrastructure Fundamentals: Master out the basics of routing protocols, port configurations, and operating system architectures before we get into the advanced testing.
- Vulnerability Assessment Workflows: We will go into how we systematically scan target networks, which in turn will identify hidden security issues and misconfigurations.
- Ethical and Legal Boundaries: We’ll dive into corporate compliance issues, white hat principles, and legal parameters related to pen testing.
How Does Hands-On Ethical Hacking Training in Pune Prepare You for Real-World Cyber Threats?
Reading about a network breach in a blog post is a different thing from when you are live at it on a corporate server. True technical authority is what you earn through constant practice in simulated environments. We have premier ethical hacking training in Pune, which has done away with the old lecture-heavy models of teaching in favor of intense simulation drills in the lab. We have you in the labs for hours at a time with Reid in reconnaissance, in network footprinting, and in system hardening procedures in safe, isolated sandbox networks.
This is an in-depth and practical approach that has you become very familiar with the exact software tools, scripting languages, and exploitation tools that live teams use daily. From the analysis of web application defects like cross-site scripting to the study of wireless network vulnerabilities and cloud security issues, we take you through the eye of an attacker. This intense method bridges the gap between theoretical study and the chaotic real-world deployment; at the program's end, you will be fully enterprise-ready.
- Attack Simulation Labs: Practice out in the field which defensive and which offensive tactics work in safe, isolated environments against live targets.
- Advanced Exploitation Tools: get in to the driver’s seat with the best in class scanning, footprinting and penetration testing software.
Which Top Industry Roles and Careers Can You Unlock After Completing the Training?
Graduating with a degree in a comprehensive security program puts you in the thick of many professional opportunities, which we see in Pune’s very dynamic job market. Once you have achieved a strong technical base through in-depth lab work, you have the exact set of skills required to step into the roles of penetration tester, corporate cybersecurity analyst, info security auditor, or security consultant. What is great about the field of cybersecurity is that these very specific roles are no longer limited to traditional IT companies; they are very much a requirement in banking, e-commerce, health care, and cloud service providers.
As you gain in the field, you will see your professional profile grow at an exponential rate for the attention of corporate recruiters. You may switch into senior engineering roles, focus on high-paying fields like cloud security architecture, or also move into a security operations center as an analyst. This career is very much so from a monetary point of view but is also what you’ll see as a very stable path out 10 years into the game as global enterprise systems continue to grow.
- SOC Analyst Placement: Work within corporate command centers, report on current issues, and help solve them immediately at the point of issue.
- Penetration Testing Specialist: Join a team that will go out and legally break into the systems we protect in order to find weak points that we can fix before the bad guys get there. Also, we will be the team that finds those hard-to-see problems and fixes them.
- Independent Security Consulting: Use your large set of skills and knowledge to start your own business that does full system overhauls, and we set the rate for our services; we work with clients worldwide. We also choose what projects we take on.
What are the practical advantages of choosing the online ethical hacking course in Pune?
For working professionals, busy engineering students, or people with chaotic personal schedules that run from one appointment to the next, our time at a physical class is a struggle. In Pune we have designed out-of-the-box online ethical hacking courses that eliminate that issue totally without a trade-off in terms of what you learn. We have done away with the boring pre-recorded modules, which left you in the dark when you had a question; instead, we have a digital platform that features live instructor-led virtual classes and real-time interactive problem solving.
This present learning platform we have designed for you is at your disposal, which allows you to grow your tech skills from anywhere without falling behind in your professional or academic life. Also, you will experience the exact same in-depth curriculum, personal mentoring, and full career support as our in-class students. Also, we see that in the tech world, which is very much a remote server and cloud-based team environment, by familiarizing yourself with our digital platform, you are in turn preparing yourself for the remote-based model that large-scale tech companies use.
- 24/7 Virtual Sandbox Access: Retain 24/7 remote access to high-end cloud-hosted security labs for when it is
- Live Instructor Interaction: Live interaction with the instructors is also available; we have experienced cyber defense professionals available at live sessions, which allow you to put forward complex questions and immediately sort out code issues.
- Seamless Schedule Integration: Advance your professional capabilities and secure industry-recognized certifications without disrupting your existing corporate or academic commitments.
Why is Customization Critical for a Corporate Ethical Hacking Course in Pune?
Modern business networks are complex and distinct and the target of automated exploit scripts and customized ransomware campaigns. We have got that we are offering generic one-size-fits-all training programs for a very different issue because what we see is each company reports out of which they have particular security issues, proprietary issues that only play out in their network structure. That is why we have built up a special corporate ethical hacking course in Pune, which is very tailor-made and very focused on the issues that your company actually has and what it does.
We work closely with your internal management teams to develop tailored workshops that train up your present IT staff, network admins, and software engineers in the thought process of digital attackers. We put your workforce through the paces of safe vulnerability assessment and identify misconfigurations and poor access privileges, and we install system hardening protocols. In doing so we foster a robust internal security culture. This proactive corporate training, which we provide, reduces your operational risk, protects your high-stakes transaction pipelines, and has your company sailing right past those tough global compliance requirements.
- Tailored Enterprise Blueprints: Align your course curriculum to what your company uses, whether that is the AWS cloud platform, physical on-site servers, or a mix of both.
- Mitigation of Compliance Risks: We put in place what it takes to train your IT staff to prevent large-scale data breaches, which in turn protects your brand image, and we also make sure they are aware of the large penalties for non-compliance.
- Internal Threat Prevention: programs that get engineering teams to identify social engineering attacks, secure coding issues, and wireless security risks before they bring down the system.
How Does SevenMentor’s Structured Approach Mitigate Common Training Risks?
In your quest to secure your cybersecurity future, it is of great importance to choose an institute that is a champion of structural transparency and academic integrity. At SevenMentor we have reworked our Ethical Hacking Course in Pune, which was dedicated to doing away with what tech students usually put up with—vague job promises, crowded classrooms, and unexpected batch shifts, which at times are hard to bear. We put forth realistic career time frames, we stand by our batch schedules, and we also use only the best from the field as faculty; thus, we make sure your academic journey is not only what you expect but also that it is a smooth and very predictable one.
Instead of a sales pitch, our Ethical Hacking Training in Pune is geared totally toward building up real, unshaken technical expertise. We are dedicated to your satisfaction, which is the same from the start of your experience until the end. We have put in place a proactive operation model, which is put forth to protect your financial, academic, and professional investment via the institutional guarantees we offer.
- Transparent Career Placement Pipelines: We do away with unrealistic promises for a more down-to-earth, aggressive career support that includes direct interview prep and puts together job offers from top IT players in Pune.
- Guaranteed Batch Modality and Structure: Also, we have the set structure and no changes to our offline class model. Once you are in our physical class, we are in a face-to-face setting; no mid-year transitions to online courses.
- Elite, Certified Cyber Professionals: are run by senior, certified professionals who dive right into practical issues rather than bore into theory.
- Strictly Capped Batch Sizes: Also, we keep batch sizes small in our in-person classes so that we can give each student one-on-one time with the instructors and the full run of our state-of-the-art labs.
How Does SevenMentor Deliver a Premium, Transparent Learning Experience in Pune?
Choosing what to put your time and energy into for advanced cybersecurity training is a large decision, which we think is best made with full transparency, which is the base of true technical education. We aren’t like the generic institutes that depend on aggressive sales tactics or set-in-stone traditional class structures. Our premier ethical hacking programs in Pune are designed from the ground up to put student success at the forefront and foster authentic career growth, and we aim for the highest academic quality. We address what is common in the training industry: large class sizes, changing schedules, and vague career promises. Instead, we present an unmarred, student-centered training environment that is designed to get the most out of your investment in education.
We have overhauled our full scale of operations to present you with a smooth, predictable, and global enterprise-grade learning experience. From our rigid batch processes to our open and high-performance career tracks, we see to it that every second you spend in our ethical hacking training in Pune adds value and technical skill.
- Honest, Merit-Based Career Pipelines: We have done away with unrealized placement schemes; instead, we present transparent, aggressive interview prep, and we put you in touch with multinational corporate hiring partners based on actual technical performance.
- Guaranteed Batch Modality Integrity: When you sign up for our in-person, hands-on classroom experience, it stays offline. We guarantee your training format will never be mixed, merged, or forced into digital streams mid-course.
- Elite, Field-Tested Cyber Instructors: You will learn from senior penetration testers who are also active in the field, which we have certified. We leave out basic theory slides in favor of live, in-depth troubleshooting.
- Strictly Capped, Low-Volume Classes: We strictly limit class sizes to guarantee a low student-to-mentor ratio, which in turn gives you that individual.
How Does Integrating Multi-Domain Tech Expertise Amplify Your Security Career Potential?
In today’s connected digital environment, a stand-alone tech skill set does not guarantee you a place in the upper rungs of the career ladder. To truly become an irreplaceable asset to corporate recruiters and to secure better salary packages, your Cybersecurity or ethical hacking course should be complemented with related tech fields. Modern corporate systems do not operate in silos; they are part of large-scale web-based networks that include auto systems and large-scale cloud and complex data infrastructure. By looking beyond the boundaries of your primary field of study into our multidisciplinary training, we help you to put together a very robust and high-performance professional profile, which in turn makes you stand out in India’s very competitive job market.
Whether scaling large banking networks’ security, designing unbreakable enterprise solutions, or developing smart defense systems, we see diversity in your tech background as the key to getting into senior engineering roles. We have designed in-depth study tracks that allow you to smoothly transition from pure defense to structural software development.
- Python & Java Infrastructure: Master backend development fundamentals to effectively audit codebases, identify syntax vulnerabilities, and write custom scripts for automated security tracking.
- Cloud Computing & DevOps Implementation: Learn the mechanics of deploying scalable applications securely while managing continuous integration loops across AWS, Azure, and modern container spaces.
- Data Science & Data Analytics Integration: Leverage statistical models and data visualization tools like Power BI to monitor complex user behavior patterns and track network performance metrics.
- Generative AI & ChatGPT Courses: Stay ahead of evolving global trends by learning to construct intelligent applications and deploy secure, AI-powered chatbot integrations.
- SAP & Salesforce Ecosystem Hardening: Specialize in locking down enterprise-level operational software and managing CRM-based web solutions against sophisticated external exploitation.
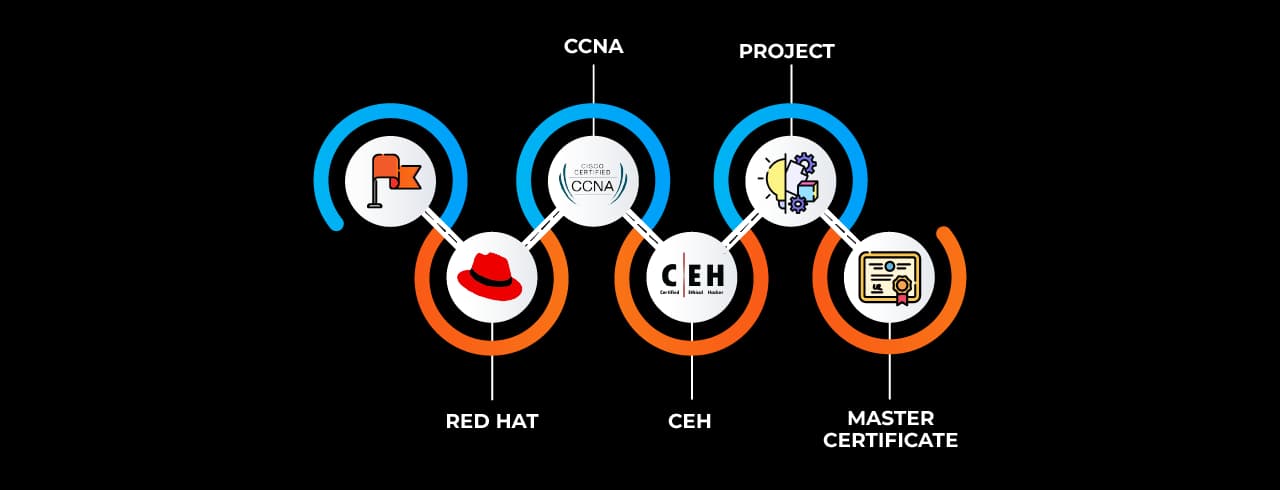
 Get Certified In Ethical Hacking And Boost Your Cybersecurity Career
Get Certified In Ethical Hacking And Boost Your Cybersecurity Career Learn Vulnerability And Penetration Testing With Expert Guidance.
Learn Vulnerability And Penetration Testing With Expert Guidance. Stay Ahead In Cybersecurity With Industry-Relevant Training.
Stay Ahead In Cybersecurity With Industry-Relevant Training.