About Ethical Hacking
What work do Ethical hackers do?
Organizations hire ethical hackers to help them find and fix security flaws in their systems. An ethical hacker needs the consent of the product owner to hack a framework in order to uncover and fix issues. Ethical hackers are employed by organizations to gain access to networks, computer systems to find and fix security problems. Hackers around the world steal 75 records every second. More ethical hackers are desperately needed, as evidenced by this. Computer security and network penetration are vital for enterprises in today's digitally-driven society. As a result, most businesses are making significant investments in ethical hacking, making employment in this industry highly sought after. White hat hackers are those who adhere to ethical standards when hacking (or a white hat hacker). Vulnerability assessment and other testing procedures that ensure the security of an organization's information systems are a specialty of this person.
What work do Ethical hackers do?
Ethical hackers are hired by businesses to assist them to uncover and repairing security weaknesses in their systems. Every second, 75 records are stolen by hackers all around the world. To find and solve flaws, an ethical hacker requires the product owner's permission to hack a framework. Organizations hire ethical hackers to obtain access to networks and computer systems in order to uncover and remedy security flaws. As proven by this, more ethical hackers are critically required. In today's digitally-driven culture, computer security and network penetration are critical for businesses. As a result, most firms are investing heavily in ethical hacking, making employment in this field extremely competitive. When it comes to hacking, white hat hackers are those that follow ethical guidelines (or white-hat hackers). This individual specializes in vulnerability assessments and other testing processes that assure the security of an organization's information systems.
How is International Certification for Ethical Hacking obtained?
The Global Certification of Certified Ethical Hacker (CEH) is provided by demonstrating knowledge of learning computer system security by checking for flaws and vulnerabilities in target systems, using the same information and tools as a fraudulent hacker, but legally and legitimately to check the security posture of a target system. Multiple-choice questions about various Ethical hacking techniques and tools are used to test the above knowledge. In order to obtain good scores in global CEH exams candidates must demonstrate the ability to apply technology and use penetration testing tools in a laboratory environment to make concessions to various simulation processes in the virtual world. The above certification is now the basis of CEH version 11.
SevenMentor’s Certified Ethical Hacking Course in Kolhapur:
In the field of IT security, ethical hacking, and networking communication, SevenMentor is a well-respected and dedicated provider of Ethical Hacking Training and solutions in the field of ethical hacking. Daily, we work on providing our students with superior knowledge and services. Our emphasis on hands-on practical Training benefits both our clients and students by helping them develop in their careers. Our main activity is to provide high-end training in Data Protection and Networking Security solution, Certified Ethical Hacking Classes in Kolhapur, and expertise in covering Black Hat engineering level topics like exploiting design, reverse code-breaking, cyberattack vulnerabilities, and malware safety.
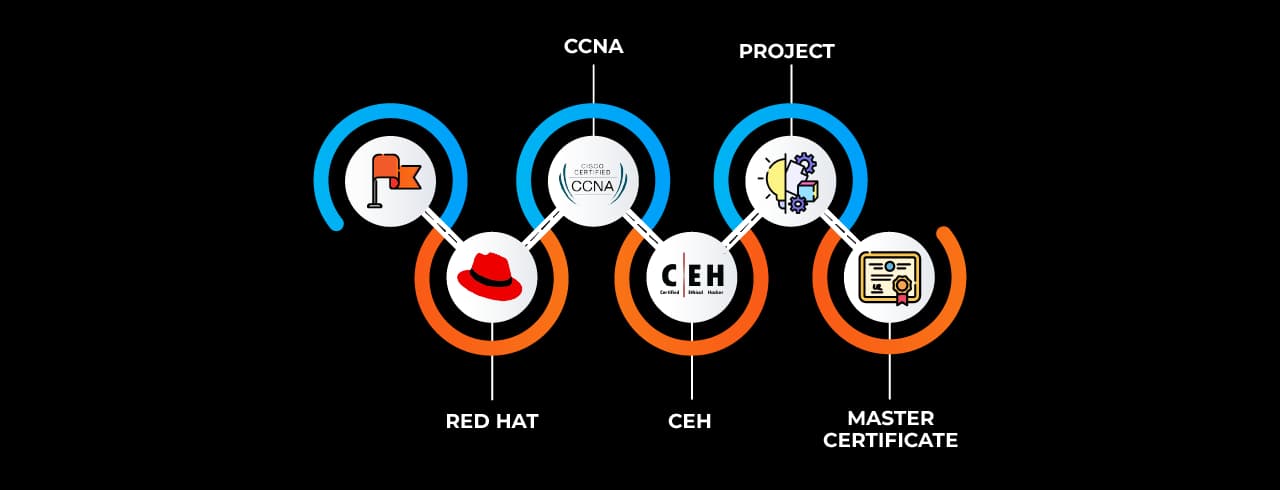
Best end-to-end Data Security Training and solutions to students from all walks of life, at an affordable price, is our objective. IT professionals today have specific needs, and we are well-versed in meeting those needs to the best of our abilities. The variety of security-specific lessons we provide allows us to provide the Training that a wide spectrum of customers need and deserve. This CEH v11 program in Kolhapur, when compared to others, stands out for several reasons including its project-based curriculum, content tailored to the needs of the industry, cutting-edge infrastructure, and extensive help with finding a job after completion of the Course.
We revise and alter our Course materials and find new and innovative approaches to prepare and equip our students for the workplace. Our real-time projects at the CEH v11 Course in Kolhapur ensure that students have a high degree of technical proficiency and are equipped for work once they enter the corporate sector. To reduce the skills gap between industry needs and student skill sets, SevenMentor is primarily concerned. This is made possible by Training that is both application-oriented and highly participative. That's why understanding the industry's quality standards and demand for highly skilled people is critical before moving further.
CEH v11 Course in Kolhapur:
Data Security and Communication, Ethical Hacking, and professional knowledge in trying to cover Black Hat level issues like Metasploit creation, code-breaking, vulnerability scanning, and so on are our core activities. We review and revise our Course materials, and we create opportunities for our students to be prepared and equipped for real-world employment scenarios. Our real-world projects ensure that students have a high level of technical competence and are ready for work when they join the Corporate world. CEH v11 Classes in Kolhapur aim to bridge the knowledge gap between industry needs and student abilities in Kolhapur. This is achieved through participatory, application-oriented Training methods. For this, only after thoroughly understanding the quality of the industry and the personnel that need to be trained do we carry forward our training. Alongside extensive curriculum and diverse training, we also provide a flexible learning timetable, therefore our syllabus is mostly made up of modular pieces. This keeps the CEH Training Course in Kolhapur flexible enough for students and working professionals while also preventing boredom by assigning entertaining tasks. Weekend and weekday batches are available at the Kolhapur facility, allowing people who are unable to attend full-time lectures on weekdays to enrol in weekend sessions. We also provide schedule rescheduling and time switching for the Course. All of these elements, together with the in-depth learning experience, enable students to receive the highest ratings and experience, CEH version 11. So come and join in the Best Ethical Hacking courses in Kolhapur.
Apart from the vast syllabus and versatile training, we also provide a flexible learning schedule and thus our syllabus consists mainly of modular elements. This helps keep the Course flexible enough for students and working professionals and inhibits loss of interest by making fun activities as assignments. The Kolhapur center has weekend and weekday batches which result in an opportunity for those who cannot attend full-time lectures on weekdays to opt for weekend batches. We also provide schedule shifting and swapping of times for the Course. All these features along with the deep learning experience help students garner the best reviews and highly experienced CEH v11 Training in Kolhapur.
Certification for Ethical Hacking Training in Kolhapur:
Our Courses all have industry-recognized accreditation. Our certifications are recognized because they meet the relevant specifications imposed by the world's biggest companies. The CEH v11 accreditation from SevenMentor Institute is useful for job placements in large corporations. We put students through rigorous examination and practice before presenting them with a lifetime valid certificate for ethical hacking. This allows SevenMentors' CEH v11 Certification Course in Kolhapur to maintain the high standard and respect it deserves. So, contact us for a free CEH v11 Training session in Kolhapur, and we will send you an invite link to attend the free demo class.
CEH Exam and Placement support after CEH v11 Course in Kolhapur:
The certified ethical hacking (CEH) v11 Course in Kolhapur will also prepare you for the EC-Council exam. Applicants who wish to take an EC-Council exam must agree to the terms of the Certification Agreement and the Non-Disclosure Agreement with the Council. Candidates should not take the exam unless they have read, comprehended, and agreed to all of the terms and conditions. When they register for the exam, candidates agree to the terms of the EC-Council Candidate Certification Agreement. EC-Council will not allow a candidate to take any of its certification exams if they do not agree to the terms of the agreement. Students are thoroughly taught and instilled with the information essential to succeed in the Global CEH v11 examinations throughout and after the CEH v11 Course at SevenMentor. Our students have a 90% probability of passing the EC Council exam as a consequence of this. We not only provide test clearing training to our pupils, but we also offer post-exam assistance, which may lead to a career in CEH hacking. Our Ethical Hacking Course in Kolhapur takes the student through different levels from basic to advanced levels for Malware and Trojan Analysis, Sniffing Concepts DDoS attacks and prevention, Botnet, Evading ID and routing networks. During and after the CEH v11 Course at SevenMentor, students are extensively explained and imbued with the knowledge necessary to succeed on tests. As a result, our pupils have a 90% chance of passing the EC Council exam. Not only do we give test clearance Training to our students, but we also provide post-exam cooperation, which could lead to a career in CEH Hacking.
SevenMentors has a job placement program that has helped over 1000 students land jobs at some of the world's most prestigious corporations. We have teachers who prepare students not just for the Ethical Hacking Course, but also for interview preparation, general ethics, and bug finding Courses. A CEH v11 Course with job placement that covers so much ground improves student employability while also instilling confidence. With SevenMentors' ethical hacking program, you can learn ethical hacking quickly and affordably while also increasing your employment prospects in India. The CEH v11 Classes in Kolhapur are a safe, effective, and most Economical Training Course in Kolhapur that will take you to the greatest employment alternatives and a terrific and skilled career in ethical hacking.
Online Classes
SevenMentor has developed a cutting-edge Online CEH v11 Course for Kolhapur professionals. We have a site for Online CEH v11 Training that incorporates modern aesthetics and a clean, clear structure after years of development and design. CEH v11 Online Classes are broken down into two sections. Students are instructed in both live and recorded sessions. Group discussions, problem-solving, and tests take place during the live sessions, which are required. The recorded sessions provide you the freedom to learn and complete the Training at your own pace and in the comfort of your own home. After students complete the Course, we issue them with a valid and up-to-date CEH v11 certification. Even in an Online setting, all students have access to the same features as those found in traditional classrooms. Students get lifetime access to reading and studying materials at the Kolhapur center thanks to the Online portal. To observe the difference in Training at SevenMentor institute, simply request a free demo through the link provided below and receive a free Online CEH v11 Course session.
Corporate Training
Employees can receive Corporate IT security and ethical hacking Training at our Institute or the company's location, depending on their preference. By providing excellent infrastructure and cutting-edge lab facilities, SevenMentor has made this feasible. More than 200 students or staff can be trained in one single on-the-job Training arena in one of our large labs. During class, students learn from the best experts in the area, and they get hands-on experience with the technology as it's being used. We carefully selected the trainers based on their extensive experience in Corporate bug hunting, large-scale vulnerability testing, and network security help in the city's Global MNCs. What distinguishes us from the competition is our commitment to professionalism and our willingness to assist industry in-house teams with IT security projects. Come and train your staff in the best Corporate Training for CEH v11 in Kolhapur with us. For our business partners in Kolhapur, we have exclusive discounts and deals.
 Get Certified In Ethical Hacking And Boost Your Cybersecurity Career
Get Certified In Ethical Hacking And Boost Your Cybersecurity Career Learn Vulnerability And Penetration Testing With Expert Guidance.
Learn Vulnerability And Penetration Testing With Expert Guidance. Stay Ahead In Cybersecurity With Industry-Relevant Training.
Stay Ahead In Cybersecurity With Industry-Relevant Training.