About Ethical Hacking
Why is Ethical Hacking important?
The importance of the professionals working in these positions cannot be overstated. They keep the company's systems, databases, and other infrastructure components in working order. They aid with the prevention of unwanted access via non-physical means. If you are a student or an IT professional interested in learning Ethical Hacking as a career option then it certainly is a good proposition for yourself.
An ethical hacker is essentially a hacker who contributes to the greater good. Whenever somebody discovers and exploits a flaw in a system, the ethical hacker informs the appropriate parties. As a result, not only does an ethical hacker save a company, but he also gets to enjoy the thrill of breaking into a system. To combat the security danger that they face, every significant corporation needs an ethical hacker on their team. If a company works with a lot of user-generated data, whether it's online communication, logistics, or something as simple as fisheries, it's vulnerable to hackers. It's even conceivable if they have a web-based presence. As a result, an ethical hacker realizes that he is being pursued by a variety of businesses, not just the IT industry. As a result, the importance of cyber security and ethical hacking has been recognized around the world. Both public and private institutions are looking for ethical hacking specialists as a result of recent data breaches. Companies want to secure their networks from thieves, thus they're willing to pay high compensation to security professionals. So there is a compelling reason to master Ethical Hacking for which you can join the best Certified Ethical Hacking Course in Aurangabad at Sevenmentor.
What are the best features of SevenMentor’s CEH v11 Course in Aurangabad?
SevenMentor has a sizable and well-known presence in Aurangabad. We have been delivering Ethical Hacking Classes in Aurangabad for a long time, making us the most experienced institution in the city. We utilize the smartest brains to teach lessons, followed by the most experienced hands to demonstrate to students how technology works and how to use it. The instructors have significant knowledge and expertise in hacking and exploiting weak software. This puts them in a strong position to educate students on how to locate vulnerabilities, detect malware, identify flaws that function as loopholes, define optimum security, and create high-reliability networks. Everything is only possible because we have the greatest trainers in the city, resulting in our pupils being equipped for real-world circumstances and possessing the optimum skill set necessary by today's standards. SevenMentor has also contributed to this by offering high-quality facilities and cutting-edge laboratory facilities. We have a large computer network with the greatest software loaded on it. The CEH v11 Training in Aurangabad facility also functions as a reading center, with a vast collection of both digital and traditional books and reference books The classrooms are huge, roomy, sanitary, and cutting-edge. Students are taught using animation software and projector-based teaching. All of this makes the complicated realm of ethical hacking more fluid and understandable.
SevenMentor is a devoted and well-recognized provider of training and solutions in the fields of IT security, ethical hacking, and networking communication. We endeavor to provide outstanding products and services to our customers daily. We give both our clients and students an edge in their career promotion by emphasizing hands-on practical training. Our primary activity is to provide high-end coaching in Data Security and Communication Safety solution learning, Qualified Penetration Testing classes, and expertise in covering Black Hat engineering level topics such as exploiting design, reverse code-breaking, cyberattack vulnerabilities, and malware safety testing. Our goal is to be a top global supplier of lower-end of the market data security training and solutions.
We understand exactly what today's IT workers want and how to satisfy those requirements to the best of our abilities. Our diverse assortment of security-specific programs enables a diverse range of clients to obtain the training they want and deserve. As compared to certain other IT security training providers, SevenMentor's CEH v11 Classes in Aurangabad stands out for its project-based curriculum, industry-specific course material, cutting-edge infrastructure, and complete placement support. We revise and alter our course materials, as well as find innovative approaches to teach and equip our students for real-world job scenarios in the business. We ensure that students have a high degree of technological competence and are prepared for work once they enter the business world through our real-time initiatives. The major objective of SevenMentor is to bridge the skills gap between industry demands and student skill sets. This is done through training that is both application-oriented and participatory. That is why, before starting, it is critical to grasp the industry's quality standards as well as the necessity for highly qualified personnel.
The CEH v11 Courses in Aurangabad is one of the most popular in the city. As a result, it is also one of SevenMentor's most affordable courses. We follow the atmosphere of Aurangabad city in giving the greatest training to students at the cheapest price and in the most efficient manner possible. We promise that our Ethical Hacking Training in Aurangabad is the greatest value for money in India.
Certification and Placement:
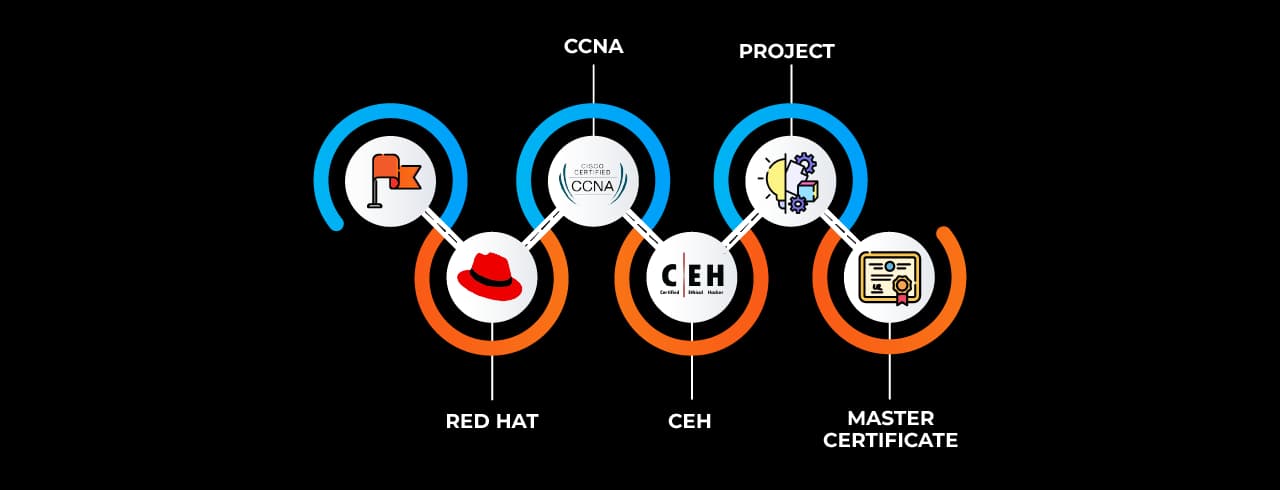
SevenMentor is an excellent choice because it is an industry-recognized and relevant course certification provider. SevenMentor will offer you a certificate once you have completed the CEH v11 Courses in Aurangabad. Participants will be able to obtain this certification by completing several projects and activities throughout the training period. The CEH v11 certification from SevenMentor is recognized and valid across India. Students are only certified after finishing the difficult curriculum, passing the examinations, and completing high-quality mini-projects.
As a result, when our students graduate, they will be well-versed in all of the required and relevant Ethical hacking themes. Because of this great dedication to quality, CEH v11 Training in Aurangabad is a guaranteed approach to increase the acceptance of your CV throughout the world. As a consequence, SevenMentor's CEH v11 Certificate Course in Aurangabad provides both complete competency and critical validation.
With every student that attends the SevenMentor, we arrange parallel recruiting campaigns, and they have assured a job with one of our partner businesses. In Aurangabad, where the firm has an on-campus presence, we have a strong HR recruitment team. All participants receive free in-person counseling and job placement help. As part of the program, all of our students attend personality and soft skill development workshops.
Our placement services have assisted our students in obtaining positions at some of the industry's most renowned businesses. As a consequence, a CEH v11 course in Aurangabad with the SevenMentor Institution will help you obtain a professional career at top worldwide organizations while also providing you with genuine and highly regarded CEH v11 certification training.
What are the Prerequisites for the CEH v11 Course in Aurangabad?
Ethical hacking as a concept is used to avoid unwanted assaults and to assist businesses in recovering from such occurrences in the case of adversaries. As a result, an ethical hacker should have a conscious mind and an inquisitive approach to computers and networking. Before enrolling students for the Ethical Hacking Training in Aurangabad, we do not need them to have a bachelor's degree or any formal background in computer sciences. Nevertheless, students will benefit from a prior understanding of coding, malware, and virus testing. We also urge that students enrolled in this course self-educate on the ideas in this module to ensure a seamless and easy learning experience.
Online Classes
SevenMentor has created a contemporary and cutting-edge Online CEH v11 course in Aurangabad. We have a site for Online CEH v11 Training in Aurangabad that incorporates current aesthetics and a clear and straightforward structure after years of research and design. CEH v11 online classes are divided into two sections. Students are trained in both live and recorded sessions. The live sessions are required for group discussions, problem-solving, and testing. The recorded lessons are a convenient method to learn and finish the training at your leisure and in the comfort of your own home. We also give students a legitimate and appropriate Online CEH v11 certification upon completion of the course. Even in an online context, all of the elements of traditional instruction are available to all students. The resources at the Aurangabad center may be accessed via the internet portal, and students have lifelong access to the institute's reading and learning materials. So, request a free demo using the link provided below and receive a free Online CEH v11 course session to experience the impact that training at SevenMentor Institution can make.
Corporate Training
At our numerous locations, we deliver Corporate IT security and Ethical Hacking Training. Our dedication to competence and readiness to support the industry's in-house team with IT Security Projects is notable. We have a staff of 50 expert trainers located across India that give proper hacking training to our corporate partners. We deal with a range of small and big organizations regularly, offering IT, software, and hardware maintenance, server maintenance courses, and business development training. The teachers are industry experts with years of hands-on experience and a thorough grasp of hacking concepts and network vulnerabilities that may be exploited. We offer our clients customized corporate services as well as collaborative sessions for the sharing of skills and knowledge across businesses. Our Corporate CEH v11 Course in Aurangabad delivers a useful and fantastic learning experience for the personnel of our client organizations, which significantly helps their company’s growth and security.
 Get Certified In Ethical Hacking And Boost Your Cybersecurity Career
Get Certified In Ethical Hacking And Boost Your Cybersecurity Career Learn Vulnerability And Penetration Testing With Expert Guidance.
Learn Vulnerability And Penetration Testing With Expert Guidance. Stay Ahead In Cybersecurity With Industry-Relevant Training.
Stay Ahead In Cybersecurity With Industry-Relevant Training.